Zero-Day Attacks: The Growing Concern Zero-day attacks have become one of the most dangerous threats in modern cybersecurity. In 2025, attackers are increasingly exploiting previously unknown software vulnerabilities—before developers even have a chance to fix them. How Zero-Day Exploits Work: Sectors Most Affected: Prevention and Protection Strategies: i4 Global Services uses AI-driven threat intelligence and […]
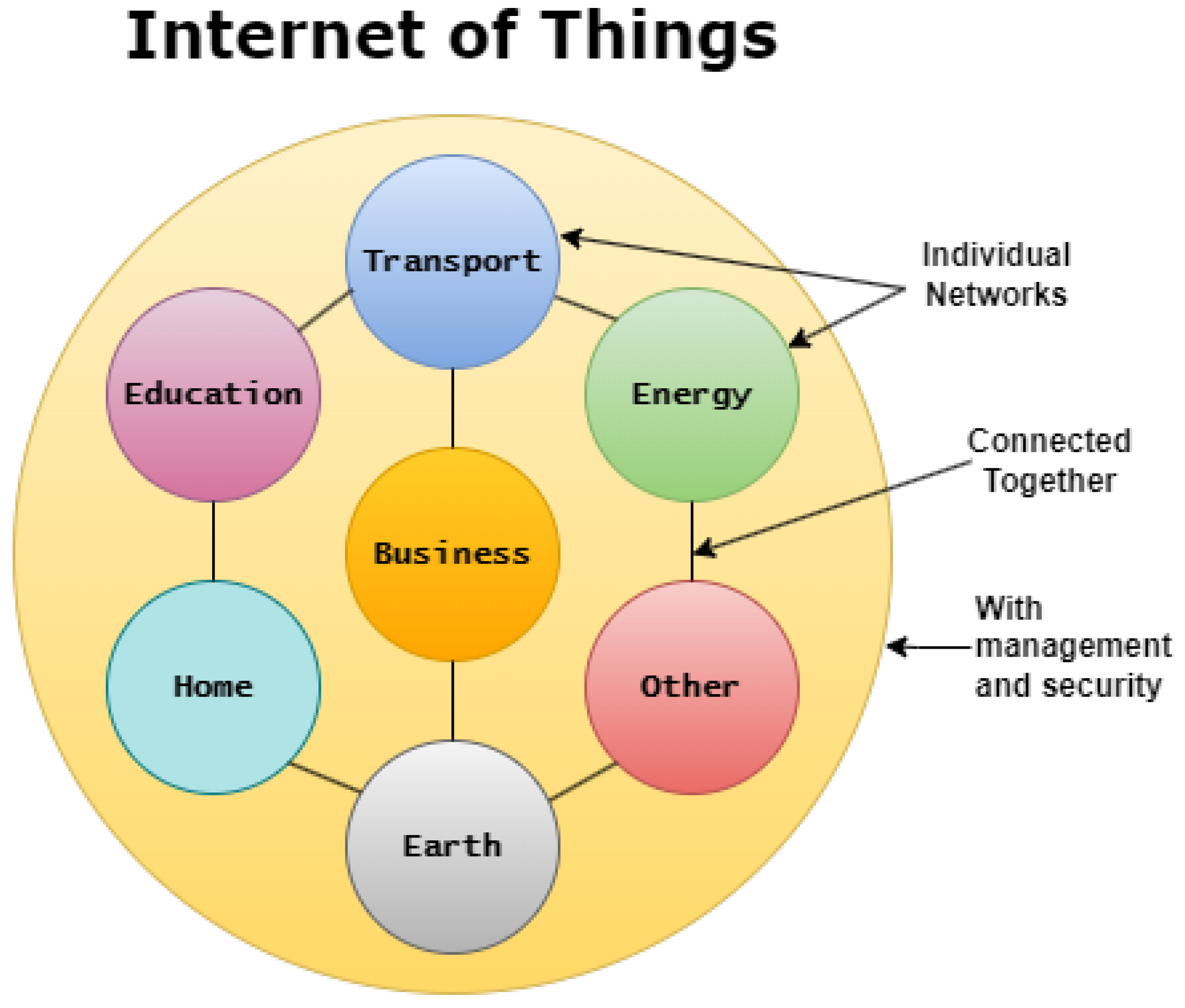
The rapid adoption of Internet of Things (IoT) devices in both personal and enterprise environments has transformed the way we live and work. From smart thermostats and connected CCTV systems to industrial sensors and healthcare monitors, IoT devices bring convenience, automation, and efficiency. However, this growing ecosystem also introduces serious security concerns. Why IoT Devices […]
In today’s hyper-connected world, cybercriminals are no longer just exploiting software vulnerabilities—they’re exploiting human behavior. Social engineering is a growing cybersecurity threat that involves manipulating individuals into divulging confidential or personal information. Unlike traditional hacking methods, social engineering doesn’t rely on complex code but on psychological tricks. What Is Social Engineering? Social engineering is the […]
In a rapidly evolving digital world where cyber threats are growing more sophisticated, ethical hacking has emerged as a critical strategy for identifying and addressing vulnerabilities before malicious attackers can exploit them. Ethical hacking—also known as penetration testing or white-hat hacking—involves authorized security experts simulating real-world cyberattacks to uncover weaknesses in systems, networks, and applications. […]